Journal of Fuzzy Systems and Control, Vol. 3, No 3, 2025 |
|
EcoSMEAL: Energy Consumption with Optimization Strategy via a Secured Smart Monitor-Alert Ensemble
Tabitha Chukwudi Aghaunor 1  , Joy Agboi 2
, Joy Agboi 2  , Eferhire Valentine Ugbotu 3
, Eferhire Valentine Ugbotu 3  , Paul Avwerosuo Onoma 4
, Paul Avwerosuo Onoma 4  ,
,
Arnold Adimabua Ojugo 5  , Christopher Chukwufunaya Odiakaose 6
, Christopher Chukwufunaya Odiakaose 6  , Andrew Okonji Eboka 7
, Andrew Okonji Eboka 7  ,
,
Peace Oguguo Ezzeh 8  , Victor Ochuko Geteloma 9
, Victor Ochuko Geteloma 9  , Amaka Patience Binitie 10
, Amaka Patience Binitie 10  , Anderson Ise Orobor 11
, Anderson Ise Orobor 11  ,
,
Blessing Uche Nwozor 12  , Patrick Ogholuwarami Ejeh 13
, Patrick Ogholuwarami Ejeh 13  , Christopher Chukwudi Onochie 14
, Christopher Chukwudi Onochie 14 
1 School of Data Intel. and Tech, Robert Morris University, Pittsburgh, PA 15108, United States
2 Department of Computer Science, Delta State University, Abraka, Delta State 330106, Nigeria
3 Department of Data Science, University of Salford, Manchester M5 4WT, United Kingdom
4, 5, 9, 11, 12 Department of Computer Science, Federal University of Petroleum Resources Effurun, Delta State 320212, Nigeria
6, 13 Department of Computer Science, Dennis Osadebay University, Asaba, Delta State 320242, Nigeria
7, 8, 10, 14 Department of Computer Science, Federal College of Education (Technical), Asaba, Delta State 320242, Nigeria
Email: 1 tabitha.aghaunor@gmail.com, 2 agboijoy0@gmail.com, 3 eferhire.ugbotu@gmail.com, 4 kenbridge14@gmail.com,
5 ojugo.arnold@fupre.edu.ng, 6 osegalaxy@gmail.com, 7 ebokaandrew@gmail.com, 8 peace.ezzeh@fcetasaba.edu.ng,
9 geteloma.victor@fupre.edu.ng, 10 amaka.binitie@fcetasaba.edu.ng, 11 orobor.anderson@fupre.edu.ng,
12 nwozor.blessing@fupre.edu.ng, 13 patrick.ejeh@dou.edu.ng, 14 xtoline2@gmail.com
*Corresponding Author
Abstract—The global demand for automation that seeks the efficient consumption and usage of energy via the adoption of embedded-fit management solutions that yield improved performance with reduced consumption has become the new norm. These explore sensor-based units in their own right with eco-friendly platforms that raise germane environmental, health, and consumption regulation(s) concerns that have today become a global issue, even when they proffer improved life standards that replace traditional solutions. Our study posits an embedded sensor design to observe environmental conditions associated with energy consumption by residential or home appliances. It utilizes a machine learning scheme and algorithm to analyze the total energy consumed by each appliance and delivers optimal consumption that reduces energy waste. The system was tested across multiple parameters and found to yield desired effectiveness, reliability, and efficiency. Our utilization of the ESP8266 and ThingSpeak is able to handle extensive inputs without significant delays or data losses. Results affirms the system ability to maintain stable performance even with more devices connected to the unit.
Keywords— IoTs; Energy consumption; Smart Monitor; Alert Ensemble; Machine Learning; Energy Optimization
Introduction
There is today, the rising trend that has birthed a genuine concern for energy consumption, health implications, and its environmental impacts, with the urgent call for the replacement of traditional energy-conservation and distribution systems with intelligent systems [1][2]. The lack of optimization and adaptability to effectively manage energy consumption has ushered in the smart grid [3], which has today as a business model [4][5] promises solutions to enhance the 2-way interaction of utilities with consumers who constantly seek to balance the consumption demands [6], [7]. With the aging infrastructure, distributed generation growth [8], increased engaged users, and adoption of innovations, there is a shift to engage in the smart-meter initiative [9][10]. Such infrastructure helps with distribution automation via phasor measurements, innovative control [11] with self-monitoring/analysis for improved energy consumption [12][13]. Smart energy systems are an integral part of the smart grid that utilizes sensing [14], computation [15], and control [16] that leans on users' interaction to satisfy users [17][18], and ensure efficient energy distribution with flexible load-shed for improved reliability, sustainability, and cost [19]. Its core technologies integrated VAR control [20], fault detection, isolation, and restoration, advanced smart metering, and dynamic load-balance for energy management with predictive maintenance [21]–[23].
Review of Literature
Governments globally are overhauling their older system with smart initiatives, with policy support, and the required funding for smart grid deployment [24]. By 2027, the global smart-grid asset market will have surpassed $125 billion, with the teeming population explosion [25], the accelerated urbanization and environmental policies enacted will all contribute as factors to heighten and tighten these fortunes as business strategies [26]. But these advances do not have the requisite policies and regulatory framework to support their exploitation therein. Thus, it ushers in technical, regulatory, economic, and consumer-behavioural challenges that must be addressed to aid the quick realization of intelligent, optimized distribution [27]. Thus, we provision the smart distribution architecture (EcoSMEAL) to help enhance the conservation, efficiency, reliability, and sustainability of energy [28].
Energy optimization in residential settings has gained significant attention due to rising energy costs and growing environmental concerns. With the complete overhaul with the budgeted N10 billion to ensure a steady energy supply at the Aso-Villa in Abuja – residential buildings account for a large proportion of global energy consumption, yet inefficiencies like energy wastage and unmonitored appliance usage persist. IoTs today offer a promising solution to these challenges, enabling real-time monitoring, automation, and optimization of energy use [29]. IoT-based smart and adaptive energy monitors facilitate the collection, transmission, and analysis of energy data for home appliances. It utilizes advanced sensors to measure energy parameters and use controllers like ESP32 to process the acquired data for further analysis [30]. Anomaly detection in usage can also empower and equip its users with improved decisions on management and traceability that reduce energy waste and consumption with lowered cost [31][32].
This consequent adoption of embedded units has also continued to pose security risks to such data access and its accompanying integrity. The cyber-risks associated with such implementation cannot be overstated. This often results in unauthorized (user) access and breaches, which are identified as barriers that dissuade the fast adoption and adaptation of smart home initiatives [33][34]. To address these concerns, our proposed model will incorporate robust security measures via encrypted communication protocols for ESP32 and secure user authentication protocols that will safeguard sensitive data, to yield a user-friendly, affordable model that is critical and crucial to its widespread adoption [35][36]. Existing systems are prohibitively expensive and complex, limiting their accessibility to average consumers [37]. Today, the need for low-cost and intuitive solutions is poised to enhance user engagement and satisfaction [38]. Our proposed model leans on a low-cost ESP32 microcontroller and cloud platforms for optimization to address security issues [39], and contributes to sustainability via reduced overall energy resources demand with minimized carbon footprint [40][41].
Study Motivation and Rationale
The study is motivated by the knowledge gaps [42][43]:
- Inefficient Use: Energy consumption in residential or home lacks proper and efficient monitoring to allow for effective management of energy resources [44][45], and leads to significant leaks. Many homes have no measure for the amount of energy consumed by each appliance(s) in their homes [46], which results in energy wastage [47]. Real-time monitoring reduces consumption with an alert mode that helps to identify inefficiencies and blind spots to optimize energy usage [48]. The presence of granular monitoring tools enables homes the capability to address such leakages effectively [39][49].
- IoT-Security: IoT monitors are besieged with security vulnerabilities ranging from data storage modes [50][51] to communication protocols [52]; Making them rife for attacks and unauthorized access [53][54]. Security often deters user adoption for IoT solutions due to the risk with sensitive data and consumption patterns, which can be exploited by adversaries for malicious intents if not adequately protected [55][56].
- High Costs and Complexity: Existing energy monitors often involve high costs, complex setups that often deter widespread adoption amongst average consumers [57][58]. But [59] notes that user-friendliness and cost also, are critical feats needed for its smooth and fast adoption in homes, as available units completely rely on expensive units and dynamic settings that render them unaffordable to budget-conscious households [60][61]. We wish to thus, deploy a target-fit solution that balances function and affordability, and does not compromise its inherent performance [62].
The study hopes to [63]:
- Design an IoT-based smart energy consumption with an optimization strategy to aid effective monitoring and alert (EcoSMEAL) targeted at residential and home energy consumption.
- Deploy EcoSMEAL using the ESP32 microcontroller.
- Fuse a robust security mechanism with encrypted data transfer and user authentication to ensure data integrity.
- Deploy the proposed system over the cloud as added security via a user interface for real-time monitoring and alert.
Evaluate/benchmark the proposed system performance with existing solutions on metrics such as throughput, efficiency, and cost.
Materials AND METHODS
Proposed Framework
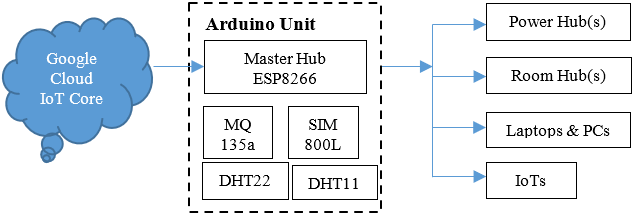
The proposed system as seen in Fig. 1, overcomes the weaknesses in the qToggle design – birthing features that enhance user convenience, energy efficiency, and scalability as a comprehensive solution fit for today’s monitor and alert needs as in Fig. 1.
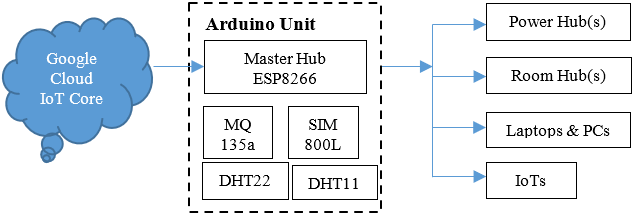
- Proposed EcoSMEAL Framework
Our EcoSMEAL addresses the inherent limitations of the qToggle framework by Stolojescu et al. [64] via its innovative solutions that lean on enhancing efficiency, scalability, and intelligence. Unlike qToggle’s use of Wi-Fi, the EcoSMEAL uses a hybrid communications protocol that integrates Wi-Fi with low-power Zigbee to encrypt communication in unit, and to reduce consumed energy and improve scalability for larger residential setups. It also features cloud integration via Google Firebase to allow for user access to real-time data remotely and to enforce robust security via its encrypted data exchange cum multi-factor authentication scheme. Other key feats by EcoSMEAL is its boosted learning that optimizes energy consumption at the various appliances as it explores predictive analytics to yield intelligent data insights [65][66] via detection of energy anomalies in consumption patterns [67]. EcoSMEAL prioritizes modularity and interoperability via seamless fusion with the existing smart home devices. Its usage of low-cost, powerful ESP32 and other sensors helps maintain affordability without compromising performance [68][69]. Furthermore, it addresses the conflict in reliability and connectivity via its redundancy mode (as a backup) and communication channel, to mitigate the impact of network disruptions [70][71].
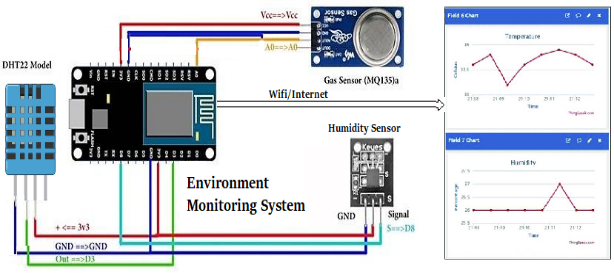
With the circuit diagram as in Fig. 2, the EcoSMEAL architecture benefits as implemented, includes:
- Extended Real-Time Processing: The unit offers full support for fast data acquisition and response, especially when handling multiple sensors simultaneously. Thus, improve real-time monitoring and alert capabilities for timely decision-making in critical scenarios.
- Scalability: It yields extensive support for unit expansion via the integration of newer and additional sensors and devices often required for both manual cum automatic configuration, increasing flexibility with reduced complexity for future upgrades.
- Improved Data Storage and Management: The proposed system's adoption of a cloud platform allows for robust, long-term data storage, and an efficient archival cum retrieval structure that yields improved historical data analysis and trend forecasting.
- Security: Its improved security protocol allows for enhanced data transfer capabilities with encrypted data mode that accounts for less susceptible and vulnerable access.
Intuitive User Interface that supports remote and mobile access for enhanced user engagement and monitoring capabilities across confined and physical locations.
- The proposed EcoSMEAL Circuit diagram
With the system incorporating a diverse range of sensors like voltage, weather, and tamper to yield richer and more heterogeneous data for improved situational intelligence with other merits as: (a) use of a multi-channel relay that offers real-time, policy-driven load control for higher grid response, (b) fused approach and paradigm that supports localized data processing and learning execution on its gateway to yield quick, resilient knowledge, (c) widely-used protocols such as DNP3, Modbus, WiFi and GSM will help users to seamlessly integrate it with the existing legacy infrastructure and networks, (d) its modular closure and open-source software customization to allow for scalable evolving needs as well as for wider coverage adoption, and (e) its use of sophisticated dashboards and databases supplements real-time monitoring and alert with retrospective analysis for transparency.
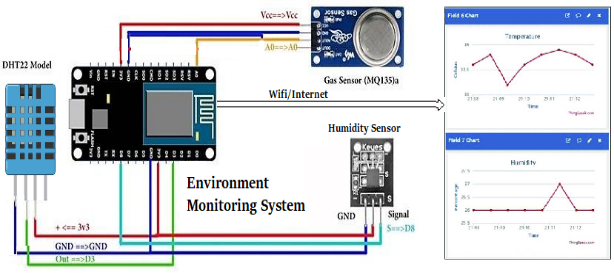
The Design Implementation
This phase transforms the design architecture into a fully operational prototype of the IoT-based monitor. It selects, integrates, and programs both hardware and software components to align with the functional and performance requirements. At the core of the hardware device lies the sensors (DHT11 and DHT22) for temperature and humidity sensing, voltage and current sensors for electrical parameter tracking, and an ESP32 with the Arduino Uno unit. Wireless comm was facilitated using the ESP8266 Wi-Fi and GSM SIM800L (to provide network availability and deployment scenarios) [72]. The units were interfaced on a custom PCB with careful attention to pin configuration, regulated voltage, and grounding settings to ensure signal integrity and safety.
Its development was initiated via Arduino IDE with codes written in embedded C/C++ to enable real-time sensor data acquisition, preprocessing, smoothing and calibration, and wireless exchange. It also includes error handling, packet form (JSON/URL), and automated reconnection protocols on network failures. Additional logic helps to handle threshold-based triggers that alert when temperature values exceed set bounds. These feats ensure the system is capable of proactive event management and monitoring. To maintain data privacy and communication integrity, the EcoSMEAL integrated the Google Firebase Cloud so as to be able to effectively receive, visualize, transmit, and store data exchanged between the system and a user device. In addition, it uses ThingSpeak to visualize a real-time graph of widgets that display dynamic sensor user data, while Firebase offers alternate functions such as structured data storage with real-time synchronization for smartphone incorporation cum integration. Its user-friendly web-based responsive interface allowed for porting to both iOS and Android platforms, deployed via HTML, JavaScript, React, or Flutter [73]. This allowed users access to live data, review historical trends, and even send control signals back to the device (e.g., reset commands or relay toggle) [74][75].
The extension/expansion capabilities of the IoT universe have continued to feature smart devices and units that foster home/societal automation, vis-à-vis to considerably easing home and office convenience [76][77]. These have, in turn, continued to attract adversarial threats and attacks. However, our utilization of the Google Firebase cloud service features a comprehensive security plan that includes data analysis, robust encryption, and device login management. These aim to supplement the stored device logs, as used for identifying attacks [78]. Implementation was designed with a modular design for improved scalability [79]. This meant that additional sensors or features such as GPS, motion detection, or camera modules could be easily added in the future without overhauling the system architecture. The use of cloud platform APIs further enabled interoperability with third-party apps/services [80], opening pathways for future fusion with predictive anomaly detection [81][82]. Overall, the implementation mode and approach ensure a robust, flexible, and real-time IoT monitor solution suitable for diverse application domains such as smart homes, industrial automation, energy metering, and environmental monitoring.
result findings and discussion
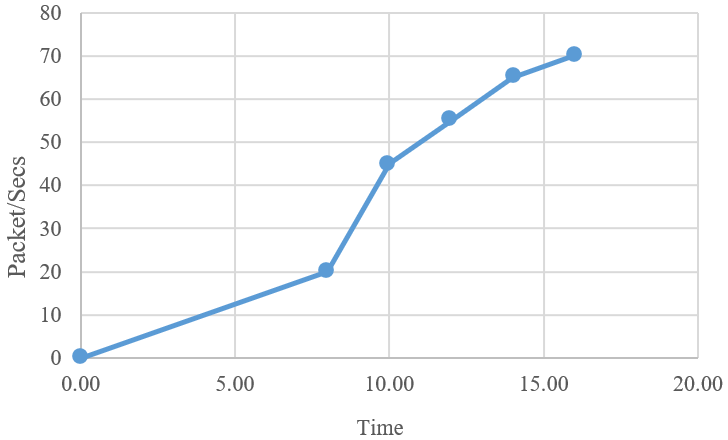
System Throughput
Throughput metrics evaluate how efficiently our model processes and transmits data packets over the network under varying operational loads [83]. It reflects the system’s data handling capacity of the IoT, especially for cases of multi-connected sensors transmitting simultaneously, as detailed in Table 1 with Fig. 3. Results yield a consistent throughput rise with a larger number of devices connected. This implies and indicates the robust data transfer capabilities of the system, which witness a peak throughput reached at 70 packets per second at the highest device load. This affirms its suitability for real-time monitoring and alert scenarios and the environment [84].
- Throughput Performance Metrics
Time | Throughput in packets per second |
08:00 | 30 |
10:00 | 45 |
12:00 | 55 |
14:00 | 65 |
16:00 | 70 |
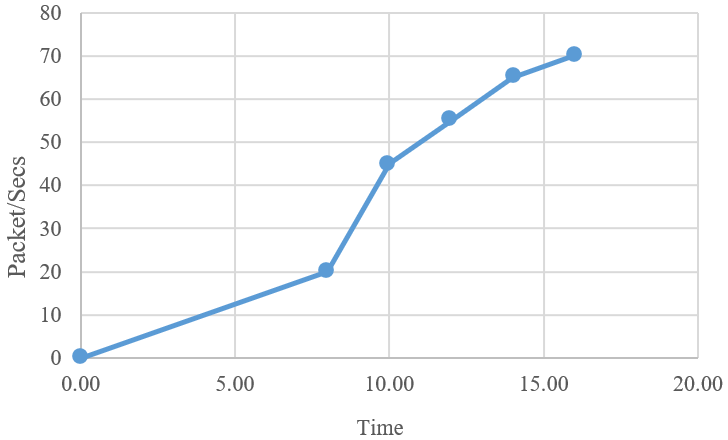
- The EcoSMEAL Throughput
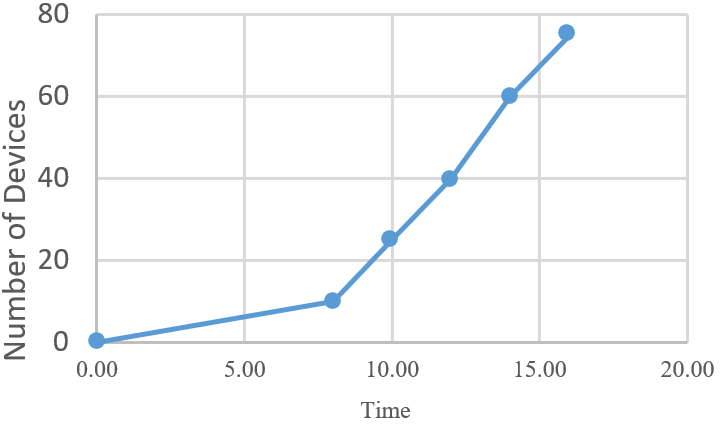
Scalability Assessment
This metric evaluates the total number of connected devices that the EcoSMEAL-IoT can simultaneously handle without inherent performance degradation. It assesses if the system can maintain data integrity [85], responsiveness, and connectivity under expanding operational load, as in Table 2 with Fig. 4. Tests at different time intervals indicate that the system scales effectively, with minimal latency and stable communication even as the number of devices increases.
- Scalability Performance Metrics
Time | Scalability in connected devices |
08:00 | 10 |
10:00 | 25 |
12:00 | 40 |
14:00 | 60 |
16:00 | 75 |
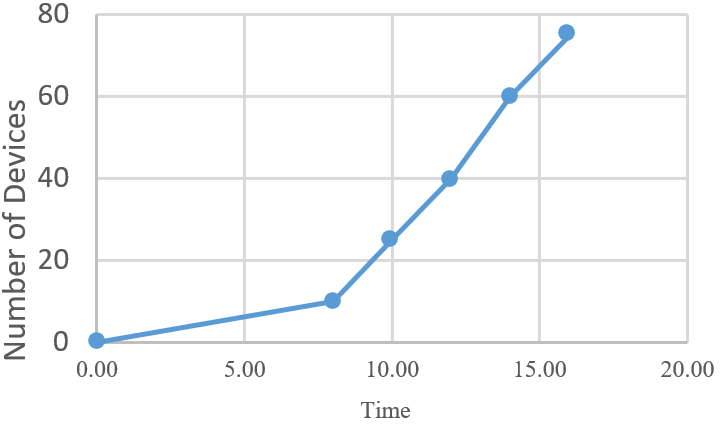
- The EcoSMEAL Scalability
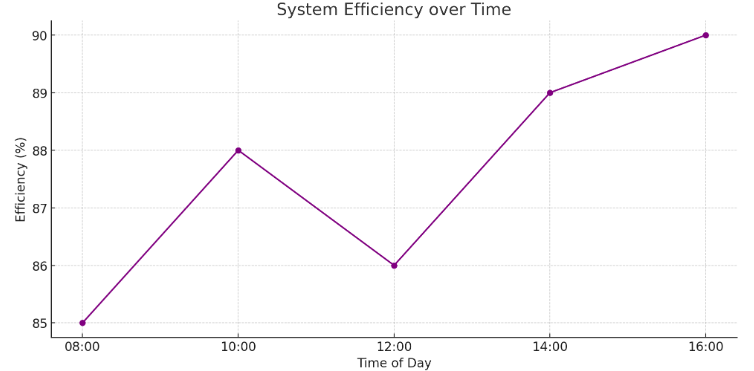
Performance Efficiency
Efficiency evaluates how optimally the system utilizes hardware resources like memory, CPU, and power during its operations cum processing [86][87]. An efficient system will maintain a consistent performance with minimal resource consumption, as is critical for IoT environments where resources are limited. Table 3 details the performance as expressed graphically in Fig. 5. Our results show that EcoSMEAL consistently maintains higher efficiency in management of system resource usage under different loads [88][89], and yields a slightly upward performance at peak operational hours, due to stable code optimization and efficient data handling mechanisms [90][91].
- Efficiency Performance Metrics
Time | Efficiency in Percentage |
08:00 | 85 |
10:00 | 88 |
12:00 | 86 |
14:00 | 89 |
16:00 | 90 |
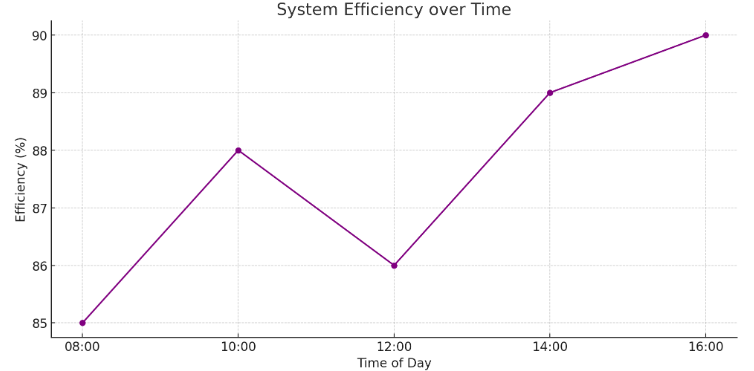
- The EcoSMEAL Efficiency
Discussion of Findings
Our system delivers promising results across multiple test parameters to yield improved effectiveness, reliability, and efficiency. It ensures ability to maintain a stable performance even with more devices connected to the unit. The utilization of the ESP8266 and ThingSpeak is able to handle extensive inputs without significant delays or data losses. Its throughput demonstrated consistent and acceptable levels of performance even with the congested (simulated), maintained network scenario that yielded regular updates to the cloud platform with minimal packet losses that ensure real-time visibility of monitored and alerted features. Its high response to data capture and transfer demonstrates that consumption remained minimal due to low-power sensors for optimized power usage. This is crucial in the real-world deployment, where battery efficiency and energy resources management are priorities. Also, its response time, which is the interval between data sensing and cloud visualization, was found within milliseconds, even under multi-threaded sensor input conditions. Its accuracy is validated via repeated trials as compared with standard instruments. The use of low-cost ESP sensors and the adoption of a robust cloud backend provisioned an efficient and scalable, responsive IoT with real-time feedback capabilities. Results demonstrate its readiness for real-world deployment and its potential enhancement via learning analytics for wider sensor support.
Conclusion
Our EcoSMEAL proves to be a viable solution for real-time data acquisition and remote supervision. Its integration of microcontrollers, sensors, and cloud allows for seamless fusion, integration, and intelligent data management that significantly enhances its monitoring features. The system is able to detect and transmit data autonomously with minimal human intervention. It has also shown high responsiveness and accuracy. It underpins its objective as a transformative, smart IoT to foster automation, adapt to new environmental regulations, and improve operational decision support. It provides an adaptable, scalable model that can be tailored to various domains and scenarios with rapidly evolving IoT deployments that incorporate physical devices for data exchange, these have continued to impact varying aspects of society’s everyday living. Our finding elucidates the urgency in prioritizing this paradigm shift vis-à-vis its deployment with notable security threats.
References
[1] G. Sabrina, Y. Khawla, G. Sabrina, B. Mabrouk, Y. Tarek, and O. Khawla, “The role of smart homes in reducing electrical energy consumption: The experience of Saudi Arabia,” International Journal of Economic Perspectives, vol. 18, no. 2, pp. 504–523, 2024, https://ijeponline.org/index.php/journal/article/view/574.
[2] A. O. Eboka et al., “Resolving Data Imbalance Using a Bi-Directional Long-Short Term Memory for Enhanced Diabetes Mellitus Detection,” Journal of Future Artificial Intelligence and Technologies, vol. 2, no. 1, pp. 95–109, 2025, https://doi.org/10.62411/faith.3048-3719-73.
[3] et al., “WiSeCart: Sensor-based Smart-Cart with Self-Payment Mode to Improve Shopping Experience and Inventory Management,” Advances in Multidisciplinary & Scientific Research Journal Publications, vol. 10, no. 1, pp. 53–74, 2024, https://doi.org/10.22624/aims/sij/v10n1p7.
[4] S. G. Jeong, Q. V. Do, and W. J. Hwang, “Short-term photovoltaic power forecasting based on hybrid quantum gated recurrent unit,” ICT Express, vol. 10, no. 3, pp. 608–613, 2024, https://doi.org/10.1016/j.icte.2023.12.005.
[5] A. A. Ojugo and A. O. Eboka, “Modeling the Computational Solution of Market Basket Associative Rule Mining Approaches Using Deep Neural Network,” Digital Technologies, vol. 3, no. 1, pp. 1–8, 2018, https://doi.org/10.12691/dt-3-1-1.
[6] C. C. Odiakaose et al., “Investigating Data Balancing Effects for Enhanced Behavioural Risk Detection in Cervical Cancer Using BiGRU: A Pilot Study,” NIPES - Journal of Science and Technology Research, vol. 7, no. 2, pp. 319–329, 2025, https://doi.org/10.37933/nipes/7.2.2025.24.
[7] Y. Himeur, A. Alsalemi, F. Bensaali, and A. Amira, “A Novel Approach for Detecting Anomalous Energy Consumption Based on Micro-Moments and Deep Neural Networks,” Cognitive Computation, vol. 12, no. 6, pp. 1381–1401, 2020, https://doi.org/10.1007/s12559-020-09764-y.
[8] A. O. Eboka et al., “Pilot study on deploying a wireless sensor-based virtual-key access and lock system for home and industrial frontiers,” International Journal of Informatics and Communication Technology, vol. 14, no. 1, pp. 287–297, 2025, https://doi.org/10.11591/ijict.v14i1.pp287-297.
[9] P. A. Onoma et al., “Investigating an Anomaly-based Intrusion Detection via Tree-based Adaptive Boosting Ensemble,” Journal of Fuzzy Systems and Control, vol. 3, no. 1, pp. 90–97, 2025, https://doi.org/10.59247/jfsc.v3i1.279.
[10] D. R. I. M. Setiadi, A. R. Muslikh, S. W. Iriananda, W. Warto, J. Gondohanindijo, and A. A. Ojugo, “Outlier Detection Using Gaussian Mixture Model Clustering to Optimize XGBoost for Credit Approval Prediction,” Journal of Computing Theories and Applications, vol. 2, no. 2, pp. 244–255, 2024, https://doi.org/10.62411/jcta.11638.
[11] E. U. Omede, A. E. Edje, M. I. Akazue, H. Utomwen, and A. A. Ojugo, “IMANoBAS: An Improved Multi-Mode Alert Notification IoT-based Anti-Burglar Defense System,” Journal of Computing Theories and Applications, vol. 1, no. 3, pp. 273–283, 2024, https://doi.org/10.62411/jcta.9541.
[12] Y. Ma, X. Chen, L. Wang, and J. Yang, “Study on Smart Home Energy Management System Based on Artificial Intelligence,” Journal of Sensors, vol. 2021, pp. 1–9, 2021, https://doi.org/10.1155/2021/9101453.
[13] J. Tian, “The Rise and Bypassing of Streaming Media,” Advances in Economics, Management and Political Sciences, vol. 57, no. 1, pp. 189–195, 2024, https://doi.org/10.54254/2754-1169/57/20230731.
[14] S. Sendra, L. García, J. Lloret, I. Bosch, and R. Vega-Rodríguez, “LoRaWAN network for fire monitoring in rural environments,” Electronics (Switzerland), vol. 9, no. 3, p. 531, 2020, https://doi.org/10.3390/electronics9030531.
[15] C. C. Odiakaose et al., “Hypertension Detection via Tree-Based Stack Ensemble with SMOTE-Tomek Data Balance and XGBoost Meta-Learner,” Journal of Future Artificial Intelligence and Technologies, vol. 1, no. 3, pp. 269–283, 2024, https://doi.org/10.62411/faith.3048-3719-43.
[16] Z. Ye, Z. O’neill, and F. Hu, “Hardware-based emulator with deep learning model for building energy control and prediction based on occupancy sensors’ data,” Information (Switzerland), vol. 12, no. 12, p. 499, 2021, https://doi.org/10.3390/info12120499.
[17] E. V. Ugbotu et al., “Transfer Learning Using a CNN Fused Random Forest for SMS Spam Detection with Semantic Normalization of Text Corpus,” NIPES - Journal of Science and Technology Research, vol. 7, no. 2, pp. 371–382, 2025, https://doi.org/10.37933/nipes/7.2.2025.29.
[18] T. C. Aghaunor et al., “Enhanced Scorch Occurrence Prediction in Foam Production via a Fusion SMOTE-Tomek Balanced Deep Learning Scheme,” NIPES - Journal of Science and Technology Research, vol. 7, no. 2, pp. 330–339, 2025, https://doi.org/10.37933/nipes/7.2.2025.25.
[19] H. Jo and Y. I. Yoon, “Intelligent smart home energy efficiency model using artificial TensorFlow engine,” Human-centric Computing and Information Sciences, vol. 8, no. 1, p. 9, 2018, https://doi.org/10.1186/s13673-018-0132-y.
[20] P. A. Onoma et al., “Voice-based Dynamic Time Warping Recognition Scheme for Enhanced Database Access Security,” Journal of Fuzzy Systems and Control, vol. 3, no. 1, pp. 81–89, 2025, https://doi.org/10.59247/jfsc.v3i1.293.
[21] A. A. Ojugo, P. O. Ejeh, O. C. Christopher, A. O. Eboka, and F. U. Emordi, “Improved distribution and food safety for beef processing and management using a blockchain-tracer support framework,” International Journal of Informatics and Communication Technology, vol. 12, no. 3, pp. 205–213, 2023, https://doi.org/10.11591/ijict.v12i3.pp205-213.
[22] A. A. Ojugo and C. O. Obruche, “Empirical Evaluation for Intelligent Predictive Models in Prediction of Potential Cancer Problematic Cases In Nigeria,” ARRUS Journal of Mathematics and Applied Science, vol. 1, no. 2, pp. 110–120, 2021, https://doi.org/10.35877/mathscience614.
[23] B. Kizilkaya, E. Ever, H. Y. Yatbaz, and A. Yazici, “An Effective Forest Fire Detection Framework Using Heterogeneous Wireless Multimedia Sensor Networks,” ACM Transactions on Multimedia Computing, Communications and Applications, vol. 18, no. 2, pp. 1–21, 2022, https://doi.org/10.1145/3473037.
[24] A. A. Ojugo and R. E. Yoro, “Computational Intelligence in Stochastic Solution for Toroidal N-Queen,” Progress in Intelligent Computing and Applications, vol. 1, no. 2, pp. 46–56, 2013, https://doi.org/10.4156/pica.vol2.issue1.4.
[25] H. H. Zeineldin, Y. A. R. I. Mohamed, V. Khadkikar, and V. Ravikumar Pandi, “A protection coordination index for evaluating distributed generation impacts on protection for meshed distribution systems,” IEEE Transactions on Smart Grid, vol. 4, no. 3, pp. 1523–1532, 2013, https://doi.org/10.1109/TSG.2013.2263745.
[26] M. Faheem, B. Raza, M. S. Bhutta, and S. H. H. Madni, “A blockchain-based resilient and secure framework for events monitoring and control in distributed renewable energy systems,” IET Blockchain, vol. 4, no. S1, pp. 644–658, 2024, https://doi.org/10.1049/blc2.12081.
[27] M. Shoaran, B. A. Haghi, M. Taghavi, M. Farivar, and A. Emami-Neyestanak, “Energy-efficient classification for resource-constrained biomedical applications,” IEEE Journal on Emerging and Selected Topics in Circuits and Systems, vol. 8, no. 4, pp. 693–707, 2018, https://doi.org/10.1109/JETCAS.2018.2844733.
[28] A. A. Ojugo, “Dependable Community-Cloud Framework for Smartphones,” American Journal of Networks and Communications, vol. 4, no. 4, p. 95, 2015, https://doi.org/10.11648/j.ajnc.20150404.13.
[29] et al., “CoDuBoTeSS: A Pilot Study to Eradicate Counterfeit Drugs via a Blockchain Tracer Support System on the Nigerian Frontier,” Advances in Multidisciplinary & Scientific Research Journal Publications, vol. 10, no. 2, pp. 53–74, 2024, https://doi.org/10.22624/aims/bij/v10n1p6.
[30] N. Rawat*, J. S. Sodhi, and R. K. Tyagi, “Deep Learning Methods for monitoring, detecting and measuring Deer Movements for Wildlife Conservation,” International Journal of Recent Technology and Engineering (IJRTE), vol. 8, no. 4, pp. 3303–3308, 2019, https://doi.org/10.35940/ijrte.d8076.118419.
[31] E. A. Aworonye, R. A. Abere, R. E. Ako, B. Nwozor, and V. O. Geteloma, “IoT-Motion electric eye ensemble for reduced power consumption in automated homes,” FUPRE Journal of Scientific and Industrial Research, vol. 8, no. 2, pp. 128–142, 2024, https://journal.fupre.edu.ng/index.php/fjsir/article/view/279.
[32] A. R. Muslikh, D. R. I. M. Setiadi, and A. A. Ojugo, “Rice disease recognition using transfer learning xception convolutional neural network,” Jurnal Teknik Informatika (Jutif), vol. 4, no. 6, pp. 1535–1540, Dec. 2023, https://doi.org/10.52436/1.jutif.2023.4.6.1529.
[33] P. K. Nandi, T. Tabassum, and M. Ahmad, “Development of an IoT-Based Automatic Remote Health Monitoring System,” Journal of Engineering Science, vol. 14, no. 2, pp. 21–30, 2024, https://doi.org/10.3329/jes.v14i2.71212.
[34] D. A. Sungheetha and D. R. Sharma R, “Real Time Monitoring and Fire Detection using Internet of Things and Cloud based Drones,” Journal of Soft Computing Paradigm, vol. 2, no. 3, pp. 168–174, 2020, https://doi.org/10.36548/jscp.2020.3.004.
[35] A. A. Ojugo, A. O. Eboka, R. E. Yoro, M. O. Yerokun, and F. N. Efozia, “Framework design for statistical fraud detection,” Mathematics and Computers in Science and Engineering Series, vol. 50, pp. 176–182, 2015, https://www.inase.org/library/2015/books/bypaper/MCSI/MCSI-33.pdf.
[36] A. A. Ojugo, E. Ugboh, C. C. Onochie, A. O. Eboka, M. O. Yerokun, and I. J. Iyawa, “Effects of Formative Test and Attitudinal Types on Students’ Achievement in Mathematics in Nigeria,” African Educational Research Journal, vol. 1, no. 2, pp. 113–117, 2013, https://eric.ed.gov/?id=EJ1216962.
[37] A. A. Ojugo and R. E. Yoro, “Migration Pattern As Threshold Parameter In The Propagation of The Covid-19 Epidemic Using An Actor-Based Model for SI-Social Graph,” JINAV: Journal of Information and Visualization, vol. 2, no. 2, pp. 93–105, 2021, https://doi.org/10.35877/454ri.jinav379.
[38] S. N. Okofu et al., “Pilot Study on Consumer Preference, Intentions and Trust on Purchasing-Pattern for Online Virtual Shops,” International Journal of Advanced Computer Science and Applications, vol. 15, no. 7, pp. 804–811, 2024, https://doi.org/10.14569/IJACSA.2024.0150780.
[39] S. A. Aessa, E. H. Ali, S. W. Shneen, and L. H. Abood, “Adaptive Fuzzy Filter Technique for Mixed Noise Removing from Sonar Images Underwater,” Journal of Fuzzy Systems and Control, vol. 2, no. 2, pp. 45–49, 2024, https://doi.org/10.59247/jfsc.v2i2.176.
[40] S. U. Okperigho, B. Nwozor, and V. O. Geteloma, “Deployment of an IoT Storage Tank Gauge and Monitor,” FUPRE Journal of Scientific and Industrial Research (FJSIR), vol. 8, no. 1, pp. 55–68, 2024, [Online]. Available: https://journal.fupre.edu.ng/index.php/fjsir/article/view/252.
[41] D.-A.-Q. Nguyen et al., “Adaptive Evaluation of LQR Control using Particle Swarm Optimization for Pendubot,” Journal of Fuzzy Systems and Control, vol. 2, no. 2, pp. 58–66, 2024, https://doi.org/10.59247/jfsc.v2i2.203.
[42] V. O. Geteloma et al., “AQuamoAS: unmasking a wireless sensor-based ensemble for air quality monitor and alert system,” Applied Engineering and Technology, vol. 3, no. 2, pp. 70–85, 2024, https://doi.org/10.31763/aet.v3i2.1409.
[43] R. E. Yoro and A. A. Ojugo, “An Intelligent Model Using Relationship in Weather Conditions to Predict Livestock-Fish Farming Yield and Production in Nigeria,” American Journal of Modeling and Optimization, vol. 7, no. 2, pp. 35–41, 2019, https://doi.org/10.12691/ajmo-7-2-1.
[44] A. A. Ojugo et al., “CoSoGMIR: A Social Graph Contagion Diffusion Framework using the Movement-Interaction-Return Technique,” Journal of Computing Theories and Applications, vol. 1, no. 2, pp. 163–173, 2023, https://doi.org/10.33633/jcta.v1i2.9355.
[45] A. D. Bhavani and N. Mangla, “A Novel Network Intrusion Detection System Based on Semi-Supervised Approach for IoT,” International Journal of Advanced Computer Science and Applications, vol. 14, no. 4, pp. 207–216, 2023, https://doi.org/10.14569/IJACSA.2023.0140424.
[46] W. L. Hsu, J. Y. Jhuang, C. S. Huang, C. K. Liang, and Y. C. Shiau, “Application of Internet of Things in a kitchen fire prevention system,” Applied Sciences (Switzerland), vol. 9, no. 17, p. 3520, 2019, https://doi.org/10.3390/app9173520.
[47] K. Okeke and S. Omojola, “Enhancing Cybersecurity Measures in Critical Infrastructure: Challenges and Innovations for Resilience,” Journal of Scientific Research and Reports, vol. 31, no. 2, pp. 474–484, 2025, https://doi.org/10.9734/jsrr/2025/v31i22868.
[48] K. Muhamada, D. R. I. M. Setiadi, U. Sudibyo, B. Widjajanto, and A. A. Ojugo, “Exploring Machine Learning and Deep Learning Techniques for Occluded Face Recognition: A Comprehensive Survey and Comparative Analysis,” Journal of Future Artificial Intelligence and Technologies, vol. 1, no. 2, pp. 160–173, 2024, https://doi.org/10.62411/faith.2024-30.
[49] A. A. Ojugo, “Predicting Behavioural Evolution on a Graph-Based Model,” Advances in Networks, vol. 3, no. 2, p. 8, 2015, https://doi.org/10.11648/j.net.20150302.11.
[50] N. R. Pratama, D. R. I. M. Setiadi, I. Harkespan, and A. A. Ojugo, “Feature Fusion with Albumentation for Enhancing Monkeypox Detection Using Deep Learning Models,” Journal of Computing Theories and Applications, vol. 2, no. 3, pp. 427–440, 2025, https://doi.org/10.62411/jcta.12255.
[51] L. R. Zuama, D. R. I. M. Setiadi, A. Susanto, S. Santosa, H.-S. Gan, and A. A. Ojugo, “High-Performance Face Spoofing Detection using Feature Fusion of FaceNet and Tuned DenseNet201,” Journal of Future Artificial Intelligence and Technologies, vol. 1, no. 4, pp. 385–400, 2025, https://doi.org/10.62411/faith.3048-3719-62.
[52] D. R. I. Moses Setiadi et al., “Single Qubit Quantum Logistic-Sine XYZ-Rotation Maps: An Ultra-Wide Range Dynamics for Image Encryption,” Computers, Materials and Continua, vol. 83, no. 2, pp. 2161–2188, 2025, https://doi.org/10.32604/cmc.2025.063729.
[53] R. E. Ako et al., “Effects of Data Resampling on Predicting Customer Churn via a Comparative Tree-based Random Forest and XGBoost,” Journal of Computing Theories and Applications, vol. 2, no. 1, pp. 86–101, 2024, https://doi.org/10.62411/jcta.10562.
[54] F. O. Aghware et al., “Enhancing the Random Forest Model via Synthetic Minority Oversampling Technique for Credit-Card Fraud Detection,” Journal of Computing Theories and Applications, vol. 1, no. 4, pp. 407–420, 2024, https://doi.org/10.62411/jcta.10323.
[55] A. A. Ojugo and D. A. Oyemade, “Predicting Diffusion Dynamics Of The Coronavirus In Nigeria Through Ties-Strength Threshold On A Cascading SI-Graph,” Technology Reports of Kansai University, vol. 62, no. 08, pp. 126–132, 2020, https://doi.org/TRKU-13-08-2020-10998.
[56] M. Oulhazzan, D. Saifaoui, S. Ettami, and A. Lilane, “Design and development of small-scale linear Fresnel solar concentrator for medium temperature applications,” Materials Today: Proceedings, vol. 30, pp. 1013–1020, 2019, https://doi.org/10.1016/j.matpr.2020.04.380.
[57] et al., “Quest for Empirical Solution to Runoff Prediction in Nigeria via Random Forest Ensemble: Pilot Study,” Advances in Multidisciplinary & Scientific Research Journal Publications, vol. 10, no. 1, pp. 73–90, 2024, https://doi.org/10.22624/aims/bhi/v10n1p8.
[58] M. I. Akazue et al., “Handling Transactional Data Features via Associative Rule Mining for Mobile Online Shopping Platforms,” International Journal of Advanced Computer Science and Applications, vol. 15, no. 3, pp. 530–538, 2024, https://doi.org/10.14569/IJACSA.2024.0150354.
[59] E. O. Okonta, A. A. Ojugo, U. R. Wemembu, and D. Ajani, “Embedding Quality Function Deployment In Software Development: A Novel Approach,” West African Journal of Industrial & Academic Research, vol. 6, no. 1, pp. 50–64, 2013, https://scispace.com/pdf/embedding-quality-function-deployment-in-software-1nkax6lobk.pdf.
[60] M. D. Okpor et al., “Pilot study on enhanced detection of cues over malicious sites using data balancing on the random forest ensemble,” Journal of Future Artificial Intelligence and Technologies, vol. 1, no. 2, pp. 109–123, 2024, https://doi.org/10.62411/faith.2024-14.
[61] D. W. S. L. Jebarani*, S. G J, and K. B, “Conservation of Energy using Object Detection Model,” International Journal of Innovative Technology and Exploring Engineering, vol. 9, no. 8, pp. 29–33, 2020, https://doi.org/10.35940/ijitee.h6435.069820.
[62] A. Mosavi and A. Bahmani, “Energy consumption prediction using machine learning; a review,” Energies, no. March, pp. 1–63, 2019, https://doi.org/10.20944/preprints201903.0131.v1.
[63] M. I. Akazue et al., “FiMoDeAL: pilot study on shortest path heuristics in wireless sensor network for fire detection and alert ensemble,” Bulletin of Electrical Engineering and Informatics, vol. 13, no. 5, pp. 3534–3543, 2024, https://doi.org/10.11591/eei.v13i5.8084.
[64] C. Stolojescu-Crisan, C. Crisan, and B. P. Butunoi, “An iot-based smart home automation system,” Sensors, vol. 21, no. 11, p. 3784, 2021, https://doi.org/10.3390/s21113784.
[65] H. Alqourabah, A. Muneer, and S. M. Fati, “A smart fire detection system using IoT technology with automatic water sprinkler,” International Journal of Electrical and Computer Engineering, vol. 11, no. 4, pp. 2994–3002, 2021, https://doi.org/10.11591/ijece.v11i4.pp2994-3002.
[66] F. O. Aghware et al., “Effects of Data Balancing in Diabetes Mellitus Detection: A Comparative XGBoost and Random Forest Learning Approach,” NIPES - Journal of Science and Technology Research, vol. 7, no. 1, pp. 1–11, 2025, https://doi.org/10.37933/nipes/7.1.2025.1.
[67] A. P. Binitie et al., “Stacked Learning Anomaly Detection Scheme with Data Augmentation for Spatiotemporal Traffic Flow,” Journal of Fuzzy Systems and Control, vol. 2, no. 3, pp. 203–214, 2024, https://doi.org/10.59247/jfsc.v2i3.267.
[68] N. Rashid, B. U. Demirel, and M. Abdullah Al Faruque, “AHAR: Adaptive CNN for Energy-Efficient Human Activity Recognition in Low-Power Edge Devices,” IEEE Internet of Things Journal, vol. 9, no. 15, pp. 13041–13051, 2022, https://doi.org/10.1109/JIOT.2022.3140465.
[69] K. Saritha, “Energy Monitoring and Theft System using IoT,” International Journal for Research in Applied Science and Engineering Technology, vol. 8, no. 6, pp. 1705–1711, 2020, https://doi.org/10.22214/ijraset.2020.6278.
[70] M. Zekić-Sušac, S. Mitrović, and A. Has, “Machine learning based system for managing energy efficiency of public sector as an approach towards smart cities,” International Journal of Information Management, vol. 58, p. 102074, 2021, https://doi.org/10.1016/j.ijinfomgt.2020.102074.
[71] D. R. I. M. Setiadi, K. Nugroho, A. R. Muslikh, S. W. Iriananda, and A. A. Ojugo, “Integrating SMOTE-Tomek and Fusion Learning with XGBoost Meta-Learner for Robust Diabetes Recognition,” Journal of Future Artificial Intelligence and Technologies, vol. 1, no. 1, pp. 23–38, 2024, https://doi.org/10.62411/faith.2024-11.
[72] V. V. Krishna, Y. Rupa, G. Koushik, T. Varun, B. V. Kiranmayee, and K. Akhil, “A Comparative Study on Authentication Vulnerabilities and Security Issues in Wearable Devices,” in Proceedings of the Fourth International Conference on Advanced Computer Engineering and Communication Systems (ICACECS 2023), 2023, vol. 18, no. Icacecs, pp. 106–116. https://doi.org/10.2991/978-94-6463-314-6_11.
[73] D. A. Oyemade and A. A. Ojugo, “A Property Oriented Pandemic Surviving Trading Model,” International Journal of Advanced Trends in Computer Science and Engineering, vol. 9, no. 5, pp. 7397–7404, 2020, https://doi.org/10.30534/ijatcse/2020/71952020.
[74] H. T. Wen, H. Y. Wu, and K. C. Liao, “Using XGBoost Regression to Analyze the Importance of Input Features Applied to an Artificial Intelligence Model for the Biomass Gasification System,” Inventions, vol. 7, no. 4, p. 126, 2022, https://doi.org/10.3390/inventions7040126.
[75] F. A.-A. Imouokhome, “A Three Tier Learning Model for Universities in Nigeria,” Journal of Technologies in Society, vol. 12, no. 2, pp. 9–20, 2016, https://doi.org/10.18848/2381-9251/cgp/v12i02/9-20.
[76] J. Govea, W. Gaibor-Naranjo, and W. Villegas-Ch, “Securing Critical Infrastructure with Blockchain Technology: An Approach to Cyber-Resilience,” Computers, vol. 13, no. 5, p. 122, 2024, https://doi.org/10.3390/computers13050122.
[77] R. E. Yoro et al., “Adaptive DDoS detection mode in software-defined SIP-VoIP using transfer learning with boosted meta-learner,” Plos One, vol. 20, no. 6 June, p. e0326571, 2025, https://doi.org/10.1371/journal.pone.0326571.
[78] B. O. Malasowe, F. O. Aghware, M. D. Okpor, E. B. Edim, R. E. Ako, and A. A. Ojugo, “Techniques and Best Practices for Handling Cybersecurity Risks in Educational Technology Environment (EdTech),” NIPES - Journal of Science and Technology Research, vol. 6, no. 2, pp. 293–311, 2024, https://doi.org/10.5281/zenodo.12617068.
[79] I. E.I., A. M.I., O. Edith, and O. Deborah, “A Framework for Smart City Model Enabled by Internet of Things (IoT),” International Journal of Computer Applications, vol. 185, no. 6, pp. 6–11, 2023, https://doi.org/10.5120/ijca2023922685.
[80] et al., “Assessing the Influence of Cybersecurity Threats and Risks on the Adoption and Growth of Digital Banking: a Systematic Literature Review,” American Journal of Advanced Technology and Engineering Solutions, vol. 1, no. 01, pp. 226–257, 2025, https://doi.org/10.63125/fh49gz18.
[81] T. Muralidharan and N. Nissim, “Improving malicious email detection through novel designated deep-learning architectures utilizing entire email,” Neural Networks, vol. 157, pp. 257-279, 2023, https://doi.org/10.1016/j.neunet.2022.09.002.
[82] L. Erhan et al., “Smart anomaly detection in sensor systems: A multi-perspective review,” Information Fusion, vol. 67, pp. 64–79, 2021, https://doi.org/10.1016/j.inffus.2020.10.001.
[83] A. O. Eboka and A. A. Ojugo, “Mitigating technical challenges via redesigning campus network for greater efficiency, scalability and robustness: A logical view,” International Journal of Modern Education and Computer Science, vol. 12, no. 6, pp. 29–45, 2020, https://doi.org/10.5815/ijmecs.2020.06.03.
[84] V. O. Geteloma et al., “Enhanced data augmentation for predicting consumer churn rate with monetization and retention strategies: a pilot study,” Applied Engineering and Technology, vol. 3, no. 1, pp. 35–51, 2024, https://doi.org/10.31763/aet.v3i1.1408.
[85] A. A. Ojugo, C. O. Obruche, and A. O. Eboka, “Quest For Convergence Solution Using Hybrid Genetic Algorithm Trained Neural Network Model For Metamorphic Malware Detection,” ARRUS Journal of Engineering and Technology, vol. 2, no. 1, pp. 12–23, 2021, https://doi.org/10.35877/jetech613.
[86] Nur Syahrina Binti Juni, Grasila Huney Wan, Siti Aisyah Nabilah Binti Banchi, Estella Blessings, Venetha A/P Loganathan, and Muhammad Faisal, “Advancements in Multi-Factor Authentication: A Quantum-Resilient and Federated Approach for Enhanced Security,” International Journal of Computer Technology and Science, vol. 1, no. 3, pp. 71–86, 2024, https://doi.org/10.62951/ijcts.v1i3.26.
[87] A. A. Ojugo and R. E. Yoro, “An Intelligent Lightweight Market Basket Associative Rule Mining for Smartphone Cloud-Based Application To Ease Banking Transaction,” Advances in Multidisciplinary & Scientific Research Journal Publication, vol. 4, no. 3, pp. 23–34, 2018, https://doi.org/10.22624/aims/v4n3p4.
[88] Raed Abdulkareem Hasan, Mustafa Mahmood Akawee, and Tole Sutikno, “Improved GIS-T model for finding the shortest paths in graphs,” Babylonian Journal of Machine Learning, vol. 2023, pp. 7–16, 2023, https://doi.org/10.58496/bjml/2023/002.
[89] A. A. Ojugo and O. Nwankwo, “forging a spectral-clustering multi-agent hybrid deep learning model to predict rainfall runoff in Nigeria,” International Journal of Innovative Science, Engineering and Technology, vol. 8, no. 3, pp. 140–147, 2021, https://ijiset.com/vol8/v8s3/IJISET_V8_I03_18.pdf.
[90] Obasuyi, D.A. et al., “NiCuSBlockIoT: Sensor-based Cargo Assets Management and Traceability Blockchain Support for Nigerian Custom Services,” Advances in Multidisciplinary & Scientific Research Journal Publications, vol. 15, no. 2, pp. 45–64, 2024, https://doi.org/10.22624/aims/cisdi/v15n2p4.
[91] R. R. Atuduhor et al., “StreamBoostE: A hybrid boosting-collaborative filter scheme for adaptive user-item recommender for streaming services,” Advances in Multidisciplinary & Scientific Research Journal Publications, vol. 10, no. 2, pp. 89–106, 2024, https://doi.org/10.22624/aims/v10n2p8.
Tabitha Chukwudi Aghaunor, EcoSMEAL: Energy Consumption with Optimization Strategy via a Secured Smart Monitor-Alert Ensemble